Medicare Secondary Payer rules determine when Medicare becomes the second payer for beneficiaries with other insurance coverage. For U.S. healthcare executives, MSP compliance represents a complex operational challenge with direct financial implications, heightened enforcement risk, and evolving regulatory requirements that demand systematic attention.
What is Medicare Secondary Payer?
Medicare Secondary Payer refers to situations where the Medicare program does not hold primary payment responsibility. When another entity—a group health plan, liability insurer, no-fault insurer, or workers’ compensation program has the obligation to pay first, Medicare becomes the secondary payer.
Enacted in 1980, MSP legislation shifted costs from Medicare to appropriate private payment sources. Before MSP, Medicare paid first for nearly all claims except those covered by Workers’ Compensation, Federal Black Lung benefits, and Veterans Administration benefits. Today, MSP provisions protect the Medicare Trust Fund by ensuring Medicare does not pay for services when other coverage is primarily responsible.
The distinction is operational, not theoretical. Providers must identify primary payers, bill them first, and only submit claims to Medicare after receiving the primary payer’s adjudication. Federal law takes precedence over state laws and private contracts. Even when state law or an insurance policy suggests Medicare should pay first, MSP provisions apply.
Why Medicare Secondary Payer Matters Now
1. Financial Impact on Medicare Trust Fund
MSP savings are substantial. According to the Department of Health and Human Services, MSP laws and regulations reduced Medicare spending by approximately $9.7 billion in fiscal year 2021. These provisions are not peripheral—they are vital to Medicare’s fiscal integrity.
The 2024 Medicare Board of Trustees’ report projects that total Part A spending will exceed incoming revenues by 2030. By 2036, insufficient funds will exist to pay full benefits. MSP recovery and coordination efforts directly address this solvency challenge.
2. Increased CMS Enforcement in 2025
CMS formalized civil money penalty (CMP) authority in October 2023. Penalties became enforceable in October 2024. CMS now randomly audits 250 submissions each calendar quarter, imposing penalties of $1,000 per day for untimely reporting.
This represents a fundamental shift. What was once primarily a compliance obligation with limited enforcement has become an area where CMS actively monitors, audits, and penalizes non-compliance. Responsible Reporting Entities (RREs)—including insurance carriers, self-insureds, and third-party administrators—face real financial exposure for reporting failures.
3. New Reporting Requirements Taking Effect
April 4, 2025 marked a watershed moment for workers’ compensation settlements. CMS now mandates Section 111 reporting of Workers’ Compensation Medicare Set-Aside Arrangement (WCMSA) data for all settlements involving Medicare beneficiaries, including those with zero-dollar allocations and settlements below the $25,000 CMS review threshold.
This gives CMS unprecedented visibility into settlement practices. The agency now knows whether future medical allocations were included in low-dollar settlements and when no WCMSA was established. This data enables enhanced coordination of benefits and identifies potential compliance gaps.
How Medicare Secondary Payer Works
Medicare remains the primary payer for beneficiaries without other health insurance coverage. However, specific situations trigger secondary payer status:
Medicare pays primary when:
- The beneficiary has no other insurance
- The beneficiary has only Medicare Supplement (Medigap) insurance
- The group health plan covering the beneficiary is from a small employer (fewer than 20 employees for working aged; fewer than 100 employees for disabled beneficiaries)
- The 30-month coordination period for ESRD has ended and other coverage remains through employment
Medicare pays secondary when:
- A beneficiary age 65 or older has group health plan coverage through current employment (their own or a spouse’s) with an employer of 20 or more employees
- A disabled beneficiary under 65 has group health plan coverage through current employment (their own or a family member’s) with an employer of 100 or more employees
- A beneficiary has ESRD and group health plan coverage during the first 30 months of Medicare eligibility
- Payment has been made or can reasonably be expected from liability insurance, no-fault insurance, or workers’ compensation
The Five Main MSP Categories
1. Working Aged: Beneficiaries age 65 or older covered by a group health plan through current employment where the employer has 20 or more employees.
2. Disability: Beneficiaries entitled to Medicare based on disability who are covered under a group health plan through current employment where the employer has 100 or more employees.
3. End-Stage Renal Disease (ESRD): Beneficiaries with ESRD who have group health plan coverage during the 30-month coordination period following Medicare eligibility.
4. Liability Insurance (including self-insurance): Coverage that may be responsible for payment when a beneficiary’s medical condition results from an accident or alleged negligence of another party.
5. No-Fault Insurance and Workers’ Compensation: Coverage for medical expenses resulting from automobile accidents (no-fault) or work-related injuries or illnesses (workers’ compensation).
The Role of the Benefits Coordination & Recovery Center (BCRC)
The BCRC administers coordination of benefits for Medicare by maintaining the Common Working File (CWF), a CMS database that stores MSP data and investigation information. The BCRC collects data from multiple sources including IRS/SSA/CMS data matches, voluntary data sharing agreements with large employers, and mandatory Section 111 reporting from insurers.
When the BCRC identifies that another payer should be primary to Medicare, it posts an MSP occurrence to Medicare’s records. This information flows to Medicare Administrative Contractors (MACs) who use it to process claims correctly.
The BCRC also manages conditional payment recovery for non-group health plan situations. When Medicare pays conditionally for services that should have been covered by liability, no-fault, or workers’ compensation insurance, the BCRC seeks reimbursement after settlement, judgment, or award.
MSP Impact on Healthcare Operations
1. Cost Implications for Providers
MSP compliance affects the bottom line in several ways. First, claims submitted incorrectly as primary when Medicare should be secondary will be denied, creating rework and delaying payment. Clean claim rates drop when MSP information is missing or inaccurate.
Second, Medicare’s secondary payment amount is calculated based on the primary payer’s allowed amount and payment. If a provider has a favorable contract with the primary payer, Medicare’s secondary payment may be minimal. Understanding this calculation is essential for accurate revenue forecasting.
Third, conditional payments create recovery obligations. If Medicare pays conditionally and later determines another payer was responsible, Medicare seeks reimbursement. Providers who received the conditional payment may face recovery demands if they also collected from the primary payer.
2. Claims Processing and Revenue Cycle Effects
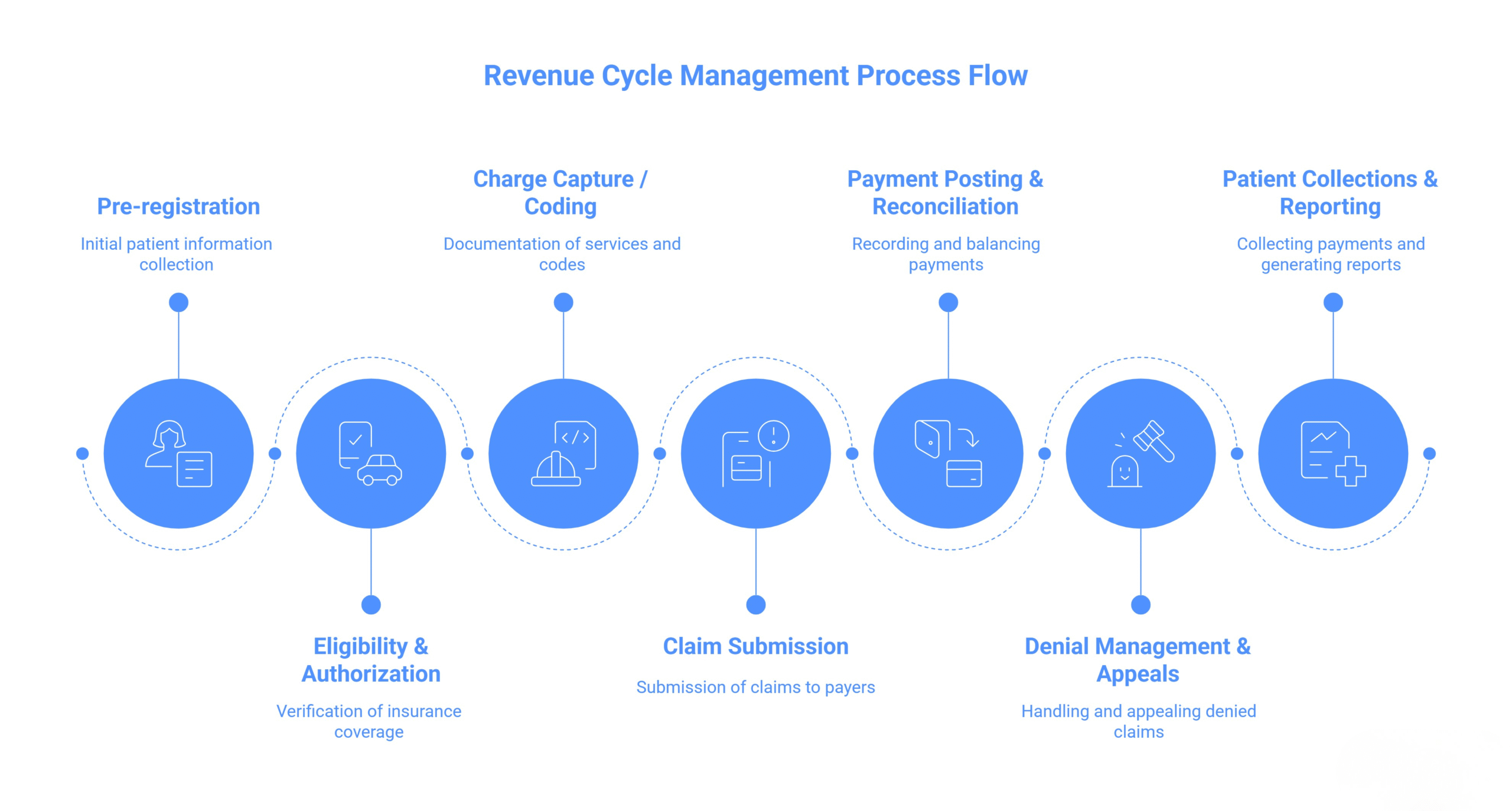
MSP adds complexity to every stage of the revenue cycle. Registration staff must collect comprehensive insurance information. Billing staff must verify which payer is primary before submitting claims. Claims must include specific MSP-related codes, condition codes, occurrence codes, and value codes to process correctly.
When Medicare is secondary, claims cannot be submitted until the primary payer has adjudicated the claim. The Explanation of Benefits (EOB) from the primary payer must accompany the Medicare claim. This sequential billing extends days in accounts receivable.
Electronic claims require proper loop and segment population for MSP information. Paper claims require specific form completion. Common billing errors include claims that don’t balance (when adjustment amounts don’t equal the total charge), missing value codes for auto/no-fault/workers’ compensation situations, and incorrect payer sequencing.
3. Compliance Requirements and Documentation Burden
Providers must make good faith efforts to determine whether Medicare is the primary or secondary payer. This requires asking beneficiaries specific questions about their insurance coverage during intake, admission, and at regular intervals for recurring services.
Documentation requirements are extensive. Providers must:
- Ask MSP-related questions at each hospital admission and outpatient visit
- Verify MSP information every 90 days for recurring outpatient services
- Maintain records of insurance information collected
- Keep documentation showing they asked the required questions, even when the beneficiary states nothing has changed
- Retain records for at least three years after the service date
For workers’ compensation situations, providers must inquire whether the beneficiary is taking legal action and bill workers’ compensation first even when the claim is disputed, unless workers’ compensation will not pay promptly.
Common MSP Mistakes Healthcare Providers Make
1. Failing to Verify Insurance at Each Encounter
The most frequent MSP error is inadequate insurance verification. Many providers collect insurance information once and never update it. Employment status changes. Spouses retire. COBRA coverage ends. Each change potentially affects MSP status.
CMS requires verification at specific intervals:
- Each inpatient hospital admission
- Each hospital outpatient visit
- Every 90 days for recurring outpatient services
Providers often misunderstand “recurring services.” These are identical services and treatments received on an outpatient basis more than once within a billing cycle. For such services, MSP information must be no older than 90 days from the service date.
2. Incomplete or Incorrect Claim Coding
MSP claims require specific coding elements. Missing or incorrect codes trigger denials. Common coding errors include:
Missing payer codes: Payer codes identify insurance coverage type. Each coverage category requires a specific payer code driven by the value codes reported on the claim.
Incorrect value codes: Value code 44 (other than accident-related) indicates the amount the provider agreed to accept from the primary payer as payment in full. Medicare uses this amount in its secondary payment calculation. Omitting VC 44 when applicable or using it incorrectly affects payment.
Missing Claim Adjustment Reason Codes (CARC): These codes explain why the primary payer’s paid amount differs from the billed amount. CMS requires CARC codes for all adjustments made by the primary payer.
Claims that don’t balance: MSP claims reject when primary claim adjustment amounts in the CAS segment plus the amount paid by the primary in the AMT segment don’t equal the total charge.
3. Not Understanding Conditional Payment Recovery
Many providers believe that once Medicare pays a claim, the transaction is complete. This is not true for MSP situations involving liability, no-fault, or workers’ compensation.
When Medicare makes a conditional payment—paying for services another payer may be responsible for—Medicare retains recovery rights. The payment is “conditional” because it must be repaid when a beneficiary receives a settlement, judgment, award, or other payment.
Providers sometimes collect from both Medicare (conditional payment) and the primary payer. Medicare then seeks recovery of the conditional payment. Understanding this recovery process is essential to avoid duplicate payments and subsequent recovery demands.
4. Missing the 90-Day Verification Window for Recurring Services
The 90-day verification requirement for recurring outpatient services is widely misunderstood. Providers often verify insurance at the start of a treatment series and assume this suffices for months of ongoing care.
When audited, CMS expects documentation showing MSP information was verified within 90 days of each service date for recurring services. “Verified” means asking the questions, not just confirming that insurance information looks the same in the system.
Providers should implement systematic prompts in their registration systems to trigger re-verification at appropriate intervals. Documentation should explicitly note that MSP questions were asked and record the beneficiary’s responses or statement that nothing has changed.
Group Health Plans vs. Non-Group Health Plans: Understanding the Difference
1. GHP Rules for Working Aged and ESRD Patients
Group Health Plans operate under specific size thresholds. For working aged beneficiaries (65 or older), the employer must have 20 or more employees for the GHP to be primary. For disabled beneficiaries under 65, the employer must have 100 or more employees.
These thresholds apply per employer, not per plan. All common law employees count, including part-time employees, regardless of whether they’re enrolled in the GHP. Separate legal entities under common ownership may be aggregated when determining size.
ESRD presents unique rules. During the first 30 months of Medicare eligibility based on ESRD, group health plan coverage through current employment remains primary. After 30 months, Medicare becomes primary. This is called the “30-month coordination period.”
If the beneficiary has ESRD and also qualifies for Medicare based on age or disability, separate rules apply depending on which entitlement came first. Providers should consult CMS guidance for these dual entitlement scenarios.
2. NGHP Coverage: Liability, No-Fault, and Workers’ Compensation
Non-Group Health Plans include liability insurance (including self-insurance), no-fault insurance, and workers’ compensation. These coverages typically arise from unexpected incidents: car accidents, work-related injuries, or injuries caused by another party’s negligence.
When an NGHP situation exists, Medicare will not pay for injury-related care if payment has been made or can reasonably be expected from the NGHP. If the NGHP insurer will not pay promptly—or if responsibility is disputed—Medicare may make conditional payments to ensure the beneficiary has access to care.
Providers must bill the NGHP first. Only after receiving the NGHP’s denial or if the NGHP will not pay promptly may the provider submit a conditional payment request to Medicare. This requires specific documentation explaining why the primary payer did not pay.
MSP Conditional Payments and Recovery Process
A conditional payment is a payment Medicare makes for services another payer may be responsible for. Medicare makes conditional payments so beneficiaries do not have to use their own money to pay medical bills while determining liability or waiting for settlements.
The payment is “conditional” because it must be repaid to Medicare when a settlement, judgment, award, or other payment is made. Medicare’s recovery rights are established by federal statute (42 U.S.C. § 1395y(b)) and override state laws and private contracts.
Conditional payments most commonly occur in liability, no-fault, and workers’ compensation situations. When a beneficiary is injured in a car accident or at work, medical care begins immediately. Determining who will ultimately pay may take months or years while liability is investigated and claims are negotiated. Medicare pays conditionally to ensure the beneficiary receives necessary care.
A. How the Recovery Process Works
The conditional payment recovery process follows several stages:
1. Reporting the case: When a liability, no-fault, or workers’ compensation case exists, it must be reported to the BCRC. This can be done by the beneficiary, their attorney, the insurer, or a provider aware of the situation. Reporting triggers the BCRC’s investigation.
2. BCRC investigation: The BCRC collects information from multiple sources including claims processors, Section 111 mandatory insurer reporting, and workers’ compensation entities. The BCRC identifies any conditional payments Medicare made that relate to the injury or illness.
3. Conditional Payment Letter (CPL) or Conditional Payment Notice (CPN): The BCRC sends a letter listing the conditional payments Medicare made and their total amount. This letter provides 30 calendar days to respond.
4. Dispute process: If the beneficiary or their representative believes certain claims should not be included, they must submit documentation supporting that position. The BCRC reviews disputes and adjusts the conditional payment amount if it agrees the claims are unrelated. This review takes up to 45 days.
5. Final demand: Once disputes are resolved and a settlement occurs, the BCRC issues a final demand letter specifying the repayment amount. This amount must be paid from the settlement proceeds.
6. Payment: Payment can be made via pay.gov using ACH, debit card, or PayPal. Failure to repay Medicare’s conditional payments can result in the debt being referred to the Department of Treasury for collection.
B. Using the Medicare Secondary Payer Recovery Portal (MSPRP)
The MSPRP is a web-based tool that allows attorneys, insurers, beneficiaries, and recovery agents to manage MSP recovery cases online. The portal provides several capabilities:
- Viewing conditional payment amounts in real time
- Submitting proof of representation and consent to release documentation
- Initiating demand letters earlier than the default 30-day period
- Disputing individual claims included in the conditional payment amount
- Requesting access to unmasked claims data
- Making electronic payments
- Tracking correspondence and case status
Registration is required before accessing the MSPRP. Users must complete identity proofing and multi-factor authentication to request access to unmasked claims data.
The MSPRP significantly accelerates the resolution process. Before the portal, everything occurred via mail and fax with extensive delays. The portal allows real-time updates and substantially reduces resolution timelines.
C. Timeline and Appeal Rights
The recovery process has defined timelines. After receiving a conditional payment letter or notice, parties have 30 days to respond. If no response is received, the BCRC may issue a demand letter.
After a demand letter is issued, beneficiaries have appeal rights. The first level of appeal is a redetermination. Redetermination requests must be filed within 120 days of receiving the demand letter. The redetermination officer reviews the case and issues a decision.
If the redetermination is unfavorable, subsequent appeal levels include reconsideration by a Qualified Independent Contractor (QIC), Administrative Law Judge hearing, Medicare Appeals Council review, and judicial review in federal district court.
Waivers of recovery are available in limited circumstances. Beneficiaries may request a waiver if recovering the conditional payment would cause financial hardship or if they were not at fault in creating the overpayment situation. Waiver requests cannot be processed until after a recovery demand letter is issued.
Old Way vs. Modern Approach to MSP Compliance
Old Way:
- Passive insurance verification at admission only
- Manual paper-based claims submission with minimal MSP coding
- Reactive response to Medicare denials and recovery demands
- Limited understanding of conditional payment obligations
- Minimal technology support beyond basic claims systems
- Siloed compliance efforts without cross-functional coordination
- Treating MSP as a billing issue rather than an enterprise risk
Modern Approach:
- Systematic verification at every encounter with automated prompts
- Electronic claims with comprehensive MSP data elements and validation edits
- Proactive identification of MSP situations before claims submission
- Clear recovery process workflows with designated staff responsibilities
- Integrated technology platforms connecting eligibility, claims, and compliance functions
- Cross-functional compliance teams involving revenue cycle, compliance, legal, and clinical leadership
- Enterprise risk management framework treating MSP as a financial and regulatory exposure requiring board-level attention
The modern approach recognizes that MSP compliance cannot be relegated to billing staff. It requires organizational commitment, technology investment, and systematic processes spanning registration through final payment resolution.
Leading organizations implement real-time eligibility checking that queries CMS systems to identify MSP indicators before services are rendered. They use automated claim scrubbing that validates MSP coding requirements before submission. They establish dedicated conditional payment coordinators who manage recovery cases and interface with the BCRC.
Most importantly, they treat MSP compliance as a strategic priority rather than an operational nuisance. Executive dashboards track MSP-related denials, recovery demands, and compliance metrics. Compliance committees review MSP performance quarterly. Leadership allocates resources to technology and training that prevent errors upstream rather than fixing them downstream.
The Next 12-36 Months: What Healthcare Leaders Should Expect
1. Enhanced CMS Monitoring and Auditing
CMS’s enforcement posture will continue strengthening. The civil money penalty framework established in 2023-2024 represents the beginning of enhanced enforcement, not its conclusion.
Expect expanded audit activity. CMS currently audits 250 quarterly submissions (1,000 annually). This may increase as CMS gains confidence in its audit processes and as agency resources grow.
Expect data analytics to drive audit selection. CMS now has unprecedented data through Section 111 reporting, including WCMSA information. The agency will identify statistical outliers—RREs with unusual reporting patterns, late submissions, or zero-dollar MSAs in circumstances suggesting underfunding. These outliers will receive closer scrutiny.
Expect False Claims Act activity to increase. The Department of Justice has shown interest in MSP non-compliance as a potential False Claims Act theory. Failure to properly identify and bill primary payers before Medicare may constitute false claims. Qui tam relators (whistleblowers) are increasingly focusing on MSP-related issues.
Healthcare leaders should prepare for this enhanced environment by establishing robust compliance programs, conducting internal audits to identify gaps, and remediating issues proactively before they become enforcement targets.
2. Technology Solutions Gaining Traction
Technology vendors are developing increasingly sophisticated MSP compliance solutions. These tools integrate with core systems to provide:
Real-time eligibility verification: Automated queries to CMS Coordination of Benefits databases during registration, surfacing MSP indicators immediately so registration staff can collect proper insurance information.
Rules-based claim validation: Pre-submission validation that checks claims for required MSP data elements, verifies coding logic, and flags potential errors before claims leave the organization.
Predictive analytics: Machine learning models that identify high-risk claims likely to generate MSP-related denials based on historical patterns.
Workflow automation: Automated routing of MSP-related tasks to appropriate staff, deadline tracking for conditional payment responses, and systematic follow-up on pending issues.
Reporting and analytics: Dashboards providing visibility into MSP denial rates, recovery demand volumes, compliance metrics, and financial impact.
Organizations should evaluate these solutions based on integration capabilities with existing systems, vendor expertise in MSP compliance, implementation support, and total cost of ownership. The right technology can significantly reduce manual effort while improving accuracy and compliance.
3. Policy Evolution and Regulatory Clarity
CMS will likely continue refining MSP guidance. The WCMSA Reference Guide has undergone multiple revisions in 2025 alone. The Section 111 User Guide updates regularly. This pattern will persist as CMS responds to industry feedback and emerging compliance issues.
Legislative activity may occur. Congressional interest in Medicare solvency creates potential for MSP-related legislation. Possible areas include:
- Standardization of WCMSA thresholds and processes
- Expansion of mandatory reporting beyond current requirements
- Enhanced CMS audit authority and penalties
- Private right of action provisions allowing Medicare beneficiaries to sue for MSP violations
Healthcare leaders should monitor regulatory developments through industry associations, CMS updates, and legal counsel. Participating in comment periods when CMS proposes rule changes allows organizations to shape policy and prepare for implementation.
The trajectory is clear: MSP compliance requirements will become more detailed, enforcement will intensify, and technology will play an increasingly central role. Organizations that prepare now will manage this transition more effectively than those waiting for problems to emerge.
Practical Takeaways for U.S. Healthcare Leaders
1. Treat MSP as an enterprise risk, not a billing issue. MSP compliance requires executive attention, cross-functional coordination, and board-level oversight. Financial exposure from penalties, recovery demands, and denied claims can be substantial.
2. Implement systematic verification processes at every encounter. One-time insurance collection at admission is insufficient. Build verification prompts into registration workflows at each service date and every 90 days for recurring services. Document that questions were asked and record responses.
3. Invest in technology that prevents errors upstream. Real-time eligibility checking, automated claim validation, and workflow management tools reduce manual effort while improving accuracy. The ROI from reduced denials and faster payment typically justifies technology investments.
4. Establish clear accountability for conditional payment management. Designate specific staff responsible for monitoring conditional payment notifications, responding to BCRC inquiries, managing disputes, and coordinating with legal counsel when necessary. These responsibilities cannot be “additional duties as assigned” for already-overloaded billing staff.
5. Conduct regular internal audits of MSP compliance. Review claims data to identify MSP-related denials, analyze root causes, and implement corrective actions. Audit documentation of insurance verification to ensure processes are being followed. Identify training needs and address gaps proactively.
6. Develop relationships with specialized MSP counsel. Complex MSP situations—particularly involving conditional payments, WCMSAs, and Section 111 reporting—require specialized legal expertise. Establish relationships with attorneys experienced in MSP compliance before problems arise.
7. Monitor regulatory developments and participate in policy discussions. CMS guidance evolves continuously. Subscribe to CMS listservs, participate in industry associations, and allocate staff time to staying current with changes. When opportunities arise to comment on proposed rules, provide input based on operational experience.